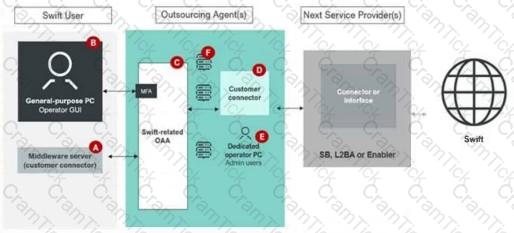
The diagram provided represents a Swift user environment with an outsourcing agent, showing various components involved in the Swift workflow. The Swift Customer Security Programme (CSP) mandates specific security controls to protect critical components, particularly those handling Swift-related data or connectivity. Let’s analyze the diagram and determine which components must be placed in asecure zoneas per theCSCF v2024.
Step 1: Understand the Secure Zone Requirement
Asecure zonein the Swift CSP context refers to a segregated, protected environment where critical Swift-related components are isolated from general-purpose systems to minimize risks. This is outlined inControl 1.1: Swift Environment Protectionof theCSCF v2024, which mandates that Swift infrastructure (e.g., messaging interfaces, connectors, and related systems) must be logically and physically separated from non-Swift systems. The secure zone ensures that only authorized systems and users can interact with Swift components.
Step 2: Analyze the Diagram and Identify Components
The diagram includes the following components:
A. Middleware server (customer connector): Labeled as Component A, this server facilitates connectivity between the Swift user’s systems and the outsourcing agent’s infrastructure.
B. General-purpose PC Operator GUI: This is a general-purpose system used by an operator to interact with the Swift environment.
C. Swift-related OAA (Operational Application Architecture): Labeled as Component C, this represents the Swift messaging interface (e.g., Alliance Access/Entry) managed by the outsourcing agent.
D. Customer connector: This component, within the outsourcing agent’s environment, interfaces directly with the Swift connector or interface.
E. Dedicated PC Admin users: This represents administrative systems used to manage the Swift environment.Additionally, there’s aConnector or Interface(SB, L2BA, or Enabler) connecting to the Swift network.
Step 3: Determine Which Components Belong in a Secure Zone
A. Middleware server (customer connector):This component facilitates connectivity between the Swift user and the outsourcing agent’s Swift-related systems. According toControl 1.1: Swift Environment Protection, any system that directly interacts with the Swift messaging infrastructure (e.g., as a connector) must reside in a secure zone to prevent unauthorized access or tampering. Since this middleware server is part of the Swift data flow, it must be in a secure zone.Conclusion: Component A must be in a secure zone.
B. General-purpose PC Operator GUI:This is a general-purpose system used by operators, not a core Swift component. TheCSCF v2024underControl 1.2: Logical Access Controlrecommends that operator systems (e.g., GUIclients) should not reside in the same secure zone as critical Swift infrastructure to avoid introducing vulnerabilities from general-purpose systems. These systems typically connect to the secure zone via controlled interfaces (e.g., VPN or jump servers) but are not part of it.Conclusion: Component B does not need to be in a secure zone.
C. Swift-related OAA:This represents the Swift messaging interface (e.g., Alliance Access/Entry), which is a core component of the Swift environment.Control 1.1explicitly requires that messaging interfaces be placed in a secure zone to protect them from external threats and ensure segregation from non-Swift systems. Since this component is directly involved in Swift message processing, it must be in a secure zone.Conclusion: Component C must be in a secure zone.
D. Customer connector:This connector interfaces directly with the Swift connector or interface (SB, L2BA, or Enabler) to facilitate communication with the Swift network. As perControl 1.1, any component that directly connects to the Swift network or handles Swift traffic must be in a secure zone to ensure end-to-end security of the communication chain. This applies to the customer connector within the outsourcing agent’s environment.Conclusion: Component D must be in a secure zone.
E. Dedicated PC Admin users:Administrative systems used to manage the Swift environment are typically not placed in the same secure zone as the operational Swift components. According toControl 1.2: Logical Access Control, administrative access should be tightly controlled and segregated, often using jump servers or bastion hosts to access the secure zone. While these systems need secure access, they are not part of the secure zone itself.Conclusion: Component E does not need to be in a secure zone.
Step 4: Conclusion and Verification
Based on theCSCF v2024requirements, the components that must be placed in a secure zone are those directly involved in Swift message processing or connectivity to the Swift network. These are:
A. Middleware server (customer connector)
C. Swift-related OAA
D. Customer connectorComponent B (general-purpose PC) and Component E (admin PC) are not required to be in the secure zone, as they are operator or administrative systems that should be segregated from the Swift operational environment.
References
Swift Customer Security Controls Framework (CSCF) v2024, Control 1.1: Swift Environment Protection.
Swift Customer Security Programme – Security Best Practices, Section: Secure Zone Configuration.
CSCF v2024, Control 1.2: Logical Access Control.