The Swift secure zone is composed of a Swift connector, a middleware server and a back office system Is the selection of only one of the above components a representative sample based on the High-Level Test Plan (HLTP) guidelines?
Is the restriction of Internet access only relevant when having Swift-related components in a secure zone?
Which operator session flows are expected to be protected in terms of confidentiality and integrity? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
The SWIFT VPN boxes are located between the Messaging and Communication interface.
•Connectivity
•Generic
•Products Cloud
•Products OnPrem
•Security
Which operator session flows are expected to be protected in terms of confidentiality and integrity? (Choose all that apply.)

Where is the implementation of multi-factor authentication deemed sufficient to support control 4.2 compliance? (Choose all that apply.)

The SWIFT user has installed its own Communication Interface on a dedicated virtual machine offered by a public cloud provider. Under which provider category does the public cloud provider fit, and what is the CSP impact? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
Which authentication methods are possible on the Alliance Interfaces? (Choose all that apply.)

A Swift user has moved from one Service Bureau to another What are the obligations of the Swift user in the CSP context?

As a Swift CSP Certified Assessor, I left the listed provider and started to work independently. Can I continue to perform CSP assessments?
An application only uses (i) the SWIFT API for reporting and gpi basic tracker calls through (ii) a tailored account not allowing business transactions management. Is this application in scope of the CSCF? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
Can a Swift user choose to implement the security controls (example: logging and monitoring) in systems which are not directly in scope of the CSCE?

A SWIFT user is not based in the same country as the assessor. The assessor would like to perform the assessment remotely. Is this permitted? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
For which reasons (as per the "CSP Independent Assessment Process for Assessors Guidelines") is it required to keep minutes of all key meetings related to a CSP assessment process (examples: kick-off, scope definition, exit meeting)? (Select all answers that apply)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
A Treasury Management System (TMS) application is installed on the same machine as the customer connector (such as MQ server) connecting towards a Service Bureau Are these applications/systems in scope of CSCF?
What are the conditions required to allow reliance on the compliance conclusion of a control assessed in the previous year? (Select all answers that apply)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
Can an internal audit department submit and approve their SWIFT user’s attestation on the KYC-SA SWIFT portal? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
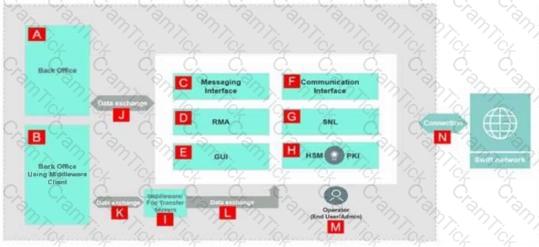
The bridging servers supporting the data exchange between the back-office and the SWIFT infrastructure are in scope of security controls (for some as advisory).
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
What is the purpose of the High-Level Test Plan (HLTP) provided by SWIFT? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
A Swift user has remediated an exception reported by the assessor. What are their obligations before updating and submitting an attestation reflecting the new compliance level?
A Treasury Management System (TMS) application is installed on the same machine as the customer connector, connecting to a Service Bureau. Are these applications/systems in scope of CSCF? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
Can an internal audit department submit and approve their Swift user's attestation on the KYC-SA Swift portal?

In the illustration, identify which components are in scope of the CSCF? (Choose all that apply.)
May an assessor rely on an ISAE 3000 report dating back 2 years to support a CSP independent assessment? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template


