Which of the following actions can be performed when the firewall identifies file anomalies?(Select All that Apply)
Predefined URL categories on Huawei firewalls reside in the URL category database delivered with the device and do not need to be manually loaded.
In a Huawei network security environment, which of the following is a key advantage of using HWTACACS over RADIUS for device management authentication?
Options:
If data filtering is configured on the firewall but is not correctly referenced in the security policy, the data that should be blocked can still be transmitted normally.
When an IPsec VPN is established in aggressive mode, AH+ESP can be used to encapsulate packets in NAT traversal scenarios.
If a Portal authentication user goes offline but neither the access device nor the RADIUS server detects this event, many problems may occur. To prevent this from occurring, the access device needs to detect a user logout immediately, delete the user entry, and instruct the RADIUS server to stop accounting. Which of the following can trigger a Portal user logout?(Select All that Apply)
When gateways are connected using GRE over IPsec, the IPsec encapsulation mode must be tunnel mode.
Which of the following conditions can be matched by PBR?(Select All that Apply)
The Nginx application is deployed on a Linux host. By checking Nginx logs, O&M engineers can obtain the complete URL information submitted by users and determine whether the Linux host is under SQL injection attacks.
HWTACACS is a centralized information exchange protocol based on the client/server structure. It uses UDP for transmission and performs authentication, authorization, and accounting for users accessing the Internet through Point-to-Point Protocol (PPP) or Virtual Private Dial-up Network (VPDN) and administrative users logging in to devices.
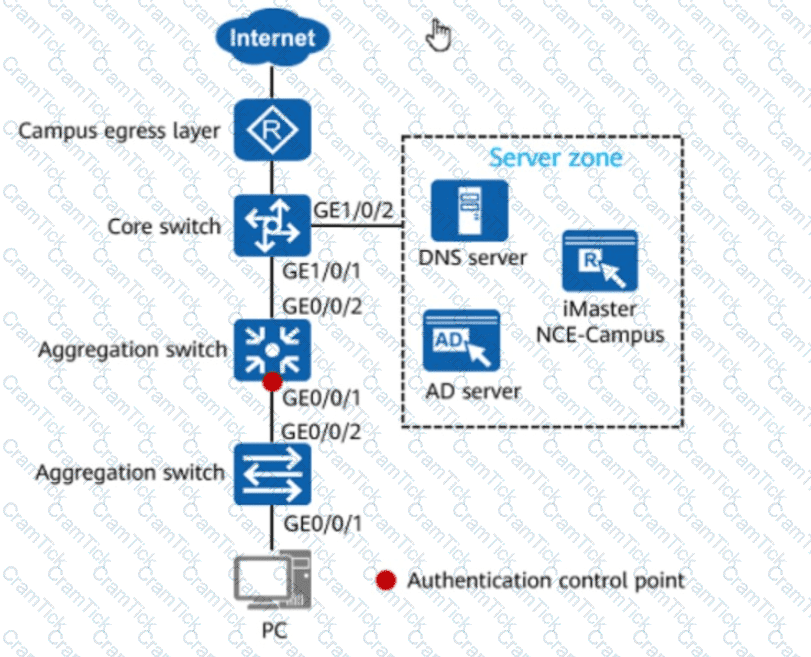
In the figure, if 802.1X authentication is used for wired users on the network, the network admission device and terminals must be connected through a Layer 2 network.
Options:
Which of the following statements is false about the restrictions on configuring bandwidth profiles in parent and child policies on a firewall?
When a user accesses the virtual gateway, the user can access the SSL VPN only after the user terminal passes the host check policy.
*In the data filtering profile on the firewall, keyword group "Keyword" is invoked in the upload direction of HTTP applications, the action is block, and the keyword group is invoked in the security policy. Given this, if the regular expression "b.d" is configured in the keyword group "Keyword,” which of the following texts can be posted by internal employees on the forum?