A cloud administrator would like to maintain file integrity checks through hashing on a cloud object store. Which of the following is MOST suitable from a performance perspective?
A systems administrator is responding to an outage in a cloud environment that was caused by a network-based flooding attack. Which of the following should the administrator configure to mitigate the attack?
A company with a worldwide presence wants to improve the user experience for its website. Which of the following can a systems administrator implement to improve download speeds and latency for the end users?
In an IaaS platform, which of the following actions would a systems administrator take FIRST to identify the scope of an incident?
Over the last couple of years, the growth of a company has required a more complex DNS and DHCP environment. Which of the following should a systems administration team implement as an appropriate solution to simplify management?
A cloud administrator needs to establish a secure connection between two different locations. Which of the following is the BEST option to implement the secure connection?
A systems administrator needs to deploy a solution to automate new application releases that come from the development team. The administrator is responsible for provisioning resources at the infrastructure layer without modifying any configurations in the application code. Which of the following would BEST accomplish this task?
An organization recently deployed a private cloud on a cluster of systems that delivers compute, network, and storage resources in a single hardware, managed by an intelligent software. Which of the following BEST describes this type of deployment?
A cloud administrator is configuring several security appliances hosted in the private laaS environment to forward the logs to a central log aggregation solution using syslog. Which of the following firewall rules should the administrator add to allow the web servers to connect to the central log collector?
A cloud security analyst needs to ensure the web servers in the public subnet allow only secure communications and must remediate any possible issue. The stateful configuration for the public web servers is as follows:
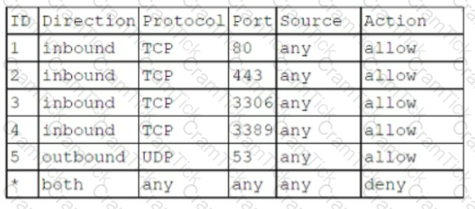
Which Of the following actions Should the analyst take to accomplish the Objective?
A cloud engineer has deployed a virtual storage appliance into a public cloud environment. The storage appliance has a NAT to a public IP address. An administrator later notices there are some strange files on the storage appliance and a large spike in network traffic on the machine. Which of the following is the MOST likely cause?
A cloud administrator configured a local cloud-resource pool lo offer 64GB of memory, 64 cores, and 640GB of storage. Thirty-two machines with identical resource allocations are started. but one machine is unable to handle requests. Which of the following is the MOST likely cause?
A technician deployed a VM with NL-SAS storage to host a critical application. Two weeks later, users have begun to report high application latency. Which of the following is the BEST action to correct the latency issue?
A systems administrator is setting up a backup solution to follow the 3-2-1 policy. Currently, the solution is set to back up from the servers to an on-site storage server. Which of the following should the administrator configure to comply with the 3-2-1 policy?
A product-based company wants to transition to a method that provides the capability to enhance the product seamlessly and keep the development iterations to a shorter time frame. Which of the following would BEST meet these requirements?
A cloud engineer, who manages workloads in a public cloud environment, uses autoscaling to maintain availability of a critical application. During a recent burst in demands, the engineer received the following error alert:
LimitedlnstanceCapacity
Which of the following is MOST likely cause of the error?
A cloud administrator needs to control the connections between a group of web servers and database servers as part of the financial application security review. Which of the following would be the BEST way to achieve this objective?
Audit and system logs are being forwarded to a syslog solution. An administrator observes that two application servers have not generated any logs for a period of three days, while others continue to send logs normally. Which of the following BEST explains what is occurring?
A DevOps team needs to provide a solution that offers isolation, portability, and scalability Which of the following would BEST meet these requirements?
A systems administrator disabled TLS 1.0 and 1.1, as well as RC4, 3DES, and AES-128 ciphers for TLS 1.2, on a web server. A client now reports being unable to access the web server, but the administrator verifies that the server is online, the web service is running, and other users can reach the server as well.
Which of the following should the administrator recommend the user do FIRST?
A systems administrator is working on the backup schedule for a critical business application that is running in a private cloud. Which of the following would help the administrator schedule the frequency of the backup job?
A company is preparing a hypervisor environment to implement a database cluster. One of the requirements is to share the disks between the nodes of the cluster to access the same LUN. Which of the following protocols Should the company use? (Select TWO)
A company is moving its entire infrastructure to the cloud. The infrastructure consists of:
100 virtual desktops
10 database servers
10 web servers
15 application servers
15 development servers
7 VDI servers
Each server, except for web, application, and database servers, needs to be on an isolated subnet. The CSP has allocated a /24 subnet. Which of the following would best divide the IP space to meet these requirements?
Options:
A systems administrator is deploying a new version of a website. The website is deployed in the cloud using a VM cluster. The administrator must then deploy the new version into one VM first. After a period of time, if there are no issues detected, a second VM will be updated. This process must continue until all the VMS are updated. Which of the following upgrade methods is being implemented?
A systems administrator is diagnosing performance issues on a web application. The web application sends thousands of extremely complex SQL queries to a database server, which has trouble retrieving the information in time. The administrator checks the database server and notes the following resource utilization:
CPU: 64%
RAM: 97%
Network throughput: 384/1000 Kbps
Disk throughput: 382,700 Kbps
The administrator also notices that the storage for the database server is consistently near its IOPS limit. Which of the following will best resolve these performance issues?
A systems administrator is planning to migrate to a cloud solution with volume-based licensing. Which of the following is most important when considering licensing costs?
A systems administrator is trying to connect to a remote KVM host. The command line appears as follows:
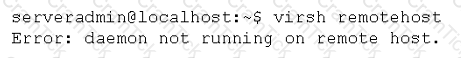
After logging in to the remote server, the administrator verifies the daemon is running. Which of the following should the administrator try NEXT?
An organization provides integration services for finance companies that use web services. A new company that sends and receives more than 100,000 transactions per second has been integrated using the web service. The other integrated companies are now reporting slowness with regard to the integration service. Which of the following is the cause of the issue?
A company has two identical environments (X and Y) running its core business application. As part of an upgrade, the X environment is patched/upgraded and tested while the Y environment is still serving the consumer workloads. Upon successful testing of the X environment, all workload is sent to this environment, and the Y environment is then upgraded before both environments start to manage the workloads. Which of the following upgrade methods is being used?
A company that requires full administrative control at the OS level is considering the use of public cloud services. Which of the following service models would BEST fit the company's requirements?
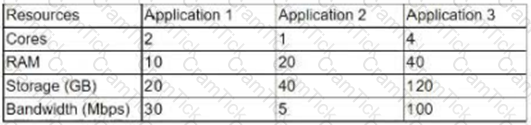
A systems administrator is asked to implement a new three-host cluster. The cloud architect specifies this should be a testing environment, and the budget is limited. The estimated resource consumption for each application is as follows:
A cloud administrator is responsible for managing a VDI environment that provides end users with access to limited applications. Which of the following should the administrator make changes to when a new application needs to be provided?
A systems administrator is responsible for upgrading operating systems on VMs that are hosted in a cloud environment. The systems administrator wants to ensure the VMs receive updates for as long as possible. Which of the following should the systems administrator choose?
A cloud administrator receives an email stating the following:
"Clients are receiving emails from our web application with non-encrypted links."
The administrator notices that links generated from the web application are opening in http://. Which of the following should be configured to redirect the traffic to https://?
A cloud administrator is investigating slow VM performance. The administrator has checked the physical server performance and has identified the host is under stress due to a peak usage workload. Which of the following is the NEXT step the administrator should complete?
A systems administrator receives a ticket stating the following:
“The programming team received an error during the process deploying applications to the container platform. The error after the containerized applications were created”
Which the following should the administrator Check FIRST?
An environment has a dual-stack infrastructure in an active-active configuration in two separate data centers. Which of the following best describes replication between the two sites?
A SaaS provider wants to maintain maximum availability for its service. Which of the following should be implemented to attain the maximum SLA?
When designing a three-node. load-balanced application, a systems administrator must ensure each node runs on a different physical server for HA purposes. Which of the following does the systems administrator need to configure?
A cloud engineer is required to move legacy systems to a public cloud. The system configuration is provided below:
Server Name
Cores
OS Disk (Used)
Data Disk (Used)
Encryption
Web1
2
500GB (45%)
1TB (20%)
OS
Web2
2
500GB (40%)
1TB (90%)
OS
App1
4
250GB (90%)
2TB (65%)
No
App2
4
250GB (70%)
2TB (95%)
No
DB1
16
250GB (25%)
4TB (65%)
Data
The public cloud provider VMs support a maximum OS disk size of 250GB and a data disk size of 2TB. Which of the following tasks will contribute to a successful migration to the cloud environment? (Select two).
A cloud engineer is deploying a server in a cloud platform. The engineer reviews a security scan report. Which of the following recommended services should be disabled? (Select TWO).
A cloud solutions architect has an environment that must only be accessed during work hours. Which of the following processes should be automated to BEST reduce cost?
A cloud security engineer needs to design an IDS/IPS solution for a web application in a single virtual private network. The engineer is considering implementing IPS protection for traffic coming from the internet. Which of the following should the engineer consider to meet this requirement?
A company that performs passive vulnerability scanning at its transit VPC has detected a vulnerability related to outdated web-server software on one of its public subnets. Which of the following can the company use to verify if this is a true positive with the least effort and cost? (Select two).
A cloud engineer is responsible for a legacy web application that runs on an on-premises VM environment. The VM environment is approaching end of life. The engineer needs to migrate the web application to the cloud as quickly as possible because the VM environment has the following limitations:
• The VM environment has a single IOGB disk.
• The VM environment still uses 10Mbps, which leaves a 100Mbps WAN connection underutilized.
• No installation media is available.
Which of the following is the best way to migrate the web application to the cloud?
A company has a large environment with multiple VPCs across three regions in a public cloud. The company is concerned about connectivity within the regions. Which of the following should the cloud administrator implement?
A cloud engineer recently set up a container image repository. The engineer wants to ensure that downloaded images are not modified in transit. Which of the following is the best method to achieve this goal?
A corporation is evaluating an offer from a CSP to take advantage of volume discounts on a shared platform. The finance department is concerned about cost allocation transparency, as the current structure splits projects into dedicated billing accounts. Which of the following can be used to address this concern?
An organization's security team must determine the likelihood of a breach on its external-facing websites. Which of the following would be best to identify the organization’s chances of incurring a breach?
After an infrastructure-as-code cloud migration to an laaS environment, the cloud engineer discovers that configurations on DB servers have drifted from the corporate standard baselines. Which of the following should the cloud engineer do to best ensure configurations are restored to the baselines?
A company is migrating a large fleet of on-premises servers into the public cloud. The number of servers is estimated to be between 800 and 900. The systems administrator is doing the network planning. Which of the following subnets should the administrator use? (Select two).
An organization's executives would like to allow access to devices that meet the corporate security compliance levels. Which of the following criteria are most important for the organization to consider? (Select two).
A systems administrator needs to implement a way for users to verify software integrity. Which of the following tools would BEST meet the administrator's needs?
One of the web applications in a public subnet is vulnerable to a newly discovered zero-day vulnerability. Which of the following actions can a security engineer perform to reduce the risk of exploitation and application downtime?
A systems administrator needs to connect the companys network to a public cloud services provider. Which of the following will BEST ensure encryption in transit for data transfers?
A cloud administrator for a retail business identified a significant month-to-month increase in the cost of storage. The current IaaS instances are hosting the organization's ERP solution. Which of the following is the most likely cause for the cost increase?
An organization has the following requirements that need to be met when implementing cloud services:
SSO to cloud infrastructure
On-premises directory service
RBAC for IT staff
Which of the following cloud models would meet these requirements?
Due to a policy change, a few of a customer’s application VMs have been migrated to synchronously replicated storage. The customer now reports that performance is lower. The systems administrator checks the resource usage and discovers CPU utilization is at 60% and available memory is at 30%.
Which of the following is the MOST likely cause?
Which of the following cloud deployment models allows a company to have full control over its IT infrastructure?
An organization purchased new servers with GPUs for render farms. The servers have limited CPU resources.
Which of the following GPU configurations will be the MOST optimal for virtualizing this environment?
An organization is running a database application on a SATA disk, and a customer is experiencing slow performance most of the time.
Which of the following should be implemented to improve application performance?
A systems administrator has migrated an internal application to a public cloud. The new web server is running under a TLS connection and has the same TLS certificate as the internal application that is deployed. However, the IT department reports that only internal users who are using new versions of the OSs are able to load the application home page.
Which of the following is the MOST likely cause of the issue?
A systems administrator notices that a piece of networking equipment is about to reach its end of support.
Which of the following actions should the administrator recommend?
A systems administrator is troubleshooting network throughput issues following a deployment. The network is currently being overwhelmed by the amount of traffic between the database and the web servers in the environment.
Which of the following should the administrator do to resolve this issue?
An organization is hosting a cloud-based web server infrastructure that provides web-hosting solutions. Sudden continuous bursts of traffic have caused the web servers to saturate CPU and network utilizations.
Which of the following should be implemented to prevent such disruptive traffic from reaching the web servers?
A cloud engineer is responsible for managing two cloud environments from different MSPs. The security department would like to inspect all traffic from the two cloud environments.
Which of the following network topology solutions should the cloud engineer implement to reduce long-term maintenance?
A technician needs to deploy two virtual machines in preparation for the configuration of a financial application next week. Which of the following cloud deployment models should the technician use?
A system administrator is migrating a bare-metal server to the cloud. Which of the following types of migration should the systems administrator perform to accomplish this task?
A systems administrator has been asked to restore a VM from backup without changing the current VM's operating state. Which of the following restoration methods would BEST fit this scenario?
An organization is required to set a custom registry key on the guest operating system.
Which of the following should the organization implement to facilitate this requirement?
An organization has multiple VLANs configured to segregate the network traffic. Following is the breakdown of the network segmentation:
Production traffic (10.10.0.0/24)
Network backup (10.20.0.0/25)
Virtual IP network (10.20.0.128/25)
The following configuration exists on the server:
The backup administrator observes that the weekly backup is failing for this server. Which of the following commands should the administrator run to identify the issue?
A systems administrator needs to convert ten physical servers to virtual.
Which of the following would be the MOST efficient conversion method for the administrator to use?
A cloud administrator is reviewing a new application implementation document. The administrator needs to make sure all the known bugs and fixes are applied, and unwanted ports and services are disabled.
Which of the following techniques would BEST help the administrator assess these business requirements?
A DevOps administrator is automating an existing software development workflow. The administrator wants to ensure that prior to any new code going into production, tests confirm the new code does not negatively impact existing automation activities.
Which of the following testing techniques would be BEST to use?
A systems administrator wants the VMs on the hypervisor to share CPU resources on the same core when feasible.
Which of the following will BEST achieve this goal?
A cloud administrator recently noticed that a number of files stored at a SaaS provider’s file-sharing service were deleted. As part of the root cause analysis, the administrator noticed the parent folder permissions were modified last week. The administrator then used a test user account and determined the permissions on the files allowed everyone to have write access.
Which of the following is the best step for the administrator to take NEXT?
A VDI administrator has received reports from the drafting department that rendering is slower than normal. Which of the following should the administrator check FIRST to optimize the performance of the VDI infrastructure?
A development team recently completed testing changes to a company's web-based CMS in the sandbox environment. The cloud administrator deployed these CMS application changes to the staging environment as part of the next phase in the release life cycle. The deployment was successful, but after deploying the CMS application, the web page displays an error message stating the application is unavailable. After reviewing the application logs, the administrator sees an error message that the CMS is unable to connect to the database. Which of the following is the BEST action for the cloud administrator to perform to resolve the issue?
Which of the following definitions of serverless computing BEST explains how it is different from using VMs?
A company is concerned about the security of its data repository that contains customer PII. A systems administrator is asked to deploy a security control that will prevent the exfiltration of such data. Which of the following should the systems administrator implement?
A systems administrator is creating a VM and wants to ensure disk space is not allocated to the VM until it is needed. Which of the following techniques should the administrator use to ensure?
A systems administrator is examining a managed hosting agreement and wants to determine how much data would be lost if a server had to be restored from backups. To which of the following metrics should the administrator refer?
A systems administrator is troubleshooting a performance issue with a virtual database server. The administrator has identified the issue as being disk related and believes the cause is a lack of IOPS on the existing spinning disk storage. Which of the following should the administrator do NEXT to resolve this issue?
Users of a public website that is hosted on a cloud platform are receiving a message indicating the connection is not secure when landing on the website. The administrator has found that only a single protocol is opened to the service and accessed through the URL https://www.comptiasite.com. Which of the following would MOST likely resolve the issue?
A company wants to check its infrastructure and application for security issues regularly. Which of the following should the company implement?
A company wants to move its environment from on premises to the cloud without vendor lock-in. Which of the following would BEST meet this requirement?
An administrator is securing a private cloud environment and wants to ensure only approved systems can connect to switches. Which of the following would be MOST useful to accomplish this task?
A cloud security analyst is implementing a vulnerability scan of the web server in the DMZ, which is running in an IaaS compute instance. The default inbound firewall settings are as follows:
Which of the following will provide the analyst with the MOST accurate report?
A cloud administrator is managing an organization's infrastructure in a public cloud. All servers are currently located in a single virtual network with a single firewall that all traffic must pass through. Per security requirements, production, QA, and development servers should not be able to communicate directly with each other. Which of the following should an administrator perform to comply with the security requirement?
A company needs a solution to find content in images. Which of the following technologies, when used in conjunction with cloud services, would facilitate the BEST solution?
A systems administrator is deploying a new storage array for backups. The array provides 1PB of raw disk space and uses 14TB nearline SAS drives. The solution must tolerate at least two failed drives in a single RAID set.
Which of the following RAID levels satisfies this requirement?
A company is utilizing a private cloud solution that is hosted within its datacenter. The company wants to launch a new business application, which requires the resources below:
The current private cloud has 30 vCPUs and 512GB RAM available. The company is looking for a quick solution to launch this application, with expected maximum sessions to be close to 24,000 at launch and an average of approximately 5,000 sessions.
Which of the following solutions would help the company accommodate the new workload in the SHORTEST amount of time and with the maximum financial benefits?
An SQL injection vulnerability was reported on a web application, and the cloud platform team needs to mitigate the vulnerability while it is corrected by the development team.
Which of the following controls will BEST mitigate the risk of exploitation?
A systems administrator needs to configure SSO authentication in a hybrid cloud environment.
Which of the following is the BEST technique to use?
A systems administrator is reviewing two CPU models for a cloud deployment. Both CPUs have the same number of cores/threads and run at the same clock speed.
Which of the following will BEST identify the CPU with more computational power?
A cloud administrator recently deployed an update to the network drivers of several servers. Following the update, one of the servers no longer responds to remote login requests. The cloud administrator investigates the issue and gathers the following information:
The cloud management console shows the VM is running and the CPU and memory utilization is at or near 0%.
The cloud management console does not show an IP address for that server.
A DNS lookup shows the hostname resolves to an IP address.
The server is a member of the same security group as the others.
The cloud administrator is able to log in remotely to the other servers without issue.
Which of the following is the MOST likely cause of the server being unavailable?
Which of the following is relevant to capacity planning in a SaaS environment?
A company has a cloud infrastructure service, and the cloud architect needs to set up a DR site.
Which of the following should be configured in between the cloud environment and the DR site?
All of a company's servers are currently hosted in one cloud MSP. The company created a new cloud environment with a different MSP. A cloud engineer is now tasked with preparing for server migrations and establishing connectivity between clouds. Which of the following should the engineer perform FIRST?
A company had a system compromise, and the engineering team resolved the issue after 12 hours. Which of the following information will MOST likely be requested by the Chief Information Officer (CIO) to understand the issue and its resolution?
An organization is developing a new solution for hosting an external website. The systems administrator needs the ability to manage the OS. Which of the following methods would be MOST suitable to achieve this objective?
A systems administrator for an e-commerce company will be migrating the company’s main website to a cloud provider. The principal requirement is that the website must be highly available.
Which of the following will BEST address this requirement?
A VDI administrator has received reports of poor application performance.
Which of the following should the administrator troubleshoot FIRST?
A cloud administrator is setting up a DR site on a different zone of the same CSP. The application servers are replicated using the VM replication, and the database replication is set up using log shipping. Upon testing the DR site, the application servers are unable to access the database servers. The administrator has verified the systems are running and are accessible from the CSP portal.
Which of the following should the administrator do to fix this issue?
An IaaS provider has numerous devices and services that are commissioned and decommissioned automatically on an ongoing basis. The cloud administrator needs to implement a solution that will help reduce administrative overhead.
Which of the following will accomplish this task?
A company recently subscribed to a SaaS collaboration service for its business users. The company also has an on-premises collaboration solution and would like users to have a seamless experience regardless of the collaboration solution being used.
Which of the following should the administrator implement?
A systems administrator is trying to establish an RDP session from a desktop to a server in the cloud. However, the connection appears to be refused even through the VM is responding to ICMP echo requests. Which of the following should the administrator check FIRST?
A cloud administrator is assigned to establish a connection between the on-premises data center and the new CSP infrastructure. The connection between the two locations must be secure at all times and provide service for all users inside the organization. Low latency is also required to improve performance during data transfer operations. Which of the following would BEST meet these requirements?
A systems administrator is using a configuration management tool to perform maintenance tasks in a system. The tool is leveraging the target system's API to perform these maintenance tasks After a number of features and security updates are applied to the target system, the configuration management tool no longer works as expected. Which of the following is the MOST likely cause of the issue?
A systems administrator is about to deploy a new VM to a cloud environment. Which of the following will the administrator MOST likely use to select an address for the VM?
After announcing a big sales promotion, an e-commerce company starts to experience a slow response on its platform that is hosted in a public cloud. When checking the resources involved, the systems administrator sees the following consumption:
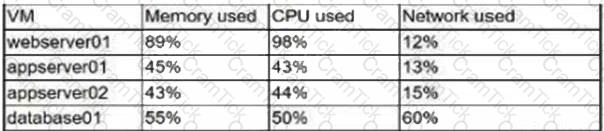
Considering all VMs were built from the same templates, which of the following actions should the administrator perform FIRST to speed up the response of the e-commerce platform?
A cloud provider wants to make sure consumers are utilizing its IaaS platform but prevent them from installing a hypervisor on the server. Which of the following will help the cloud provider secure the environment and limit consumers’ activity?
An administrator has been informed that some requests are taking a longer time to respond than other requests of the same type. The cloud consumer is using multiple network service providers and is performing link load balancing for bandwidth aggregation. Which of the following commands will help the administrator understand the possible latency issues?
A support engineer wants to prevent users from running malware on several IaaS compute instances. Which of the following will BEST achieve this objective?
Users are experiencing slow response times from an intranet website that is hosted on a cloud platform. There is a site-to-site VPN connection to the cloud provider over a link of 100Mbps.
Which of the following solutions will resolve the issue the FASTEST?
A systems administrator has migrated a web application to the cloud with a synchronous uplink speed of 100Mbps. After the migration, the administrator receives reports of slow connectivity to the web application. The administrator logs into the firewall and notices the WAN port is transmitting at a constant 12.5MBps. Which of the following BEST explains the reason for the issue?
An engineer is responsible for configuring a new firewall solution that will be deployed in a new public cloud environment. All traffic must pass through the firewall. The SLA for the firewall is 99.999%. Which of the following should be deployed?
After a few new web servers were deployed, the storage team began receiving incidents in their queue about the web servers. The storage administrator wants to verify the incident tickets that should have gone to the web server team. Which of the following is the MOST likely cause of the issue?
Which of the following would be the BEST option for discussion of what individuals should do in an incident response or disaster recovery scenario?
A resource pool in a cloud tenant has 90 GB of memory and 120 cores. The cloud administrator needs to maintain a 30% buffer for resources for optimal performance of the hypervisor. Which of the following would all ow for the maximum number of two-core machines with equal memory?
A systems administrator is working in a globally distributed cloud environment. After a file server VM was moved to another region, all users began reporting slowness when saving files. Which of the following is the FIRST thing the administrator should check while troubleshooting?
A company needs to rehost its ERP system to complete a datacenter migration to the public cloud. The company has already migrated other systems and configured VPN connections.
Which of the following MOST likely needs to be analyzed before rehosting the ERP?
After accidentally uploading a password for an IAM user in plain text, which of the following should a cloud administrator do FIRST? (Choose two.)
During a security incident, an laaS compute instance is detected to send traffic to a host related to cryptocurrency mining. The security analyst handling the incident determines the scope of the incident is limited to that particular instance. Which of the following should the security analyst do NEXT?
An enterprise recently upgraded the memory of its on-premises VMs from 8GB to 16GB. However, users are not experiencing any performance benefit. Which of the following is the MOST likely reason?
A cloud administrator has created a new asynchronous workflow lo deploy VMs to the cloud in bulk. When the workflow is tested for a single VM, it completes successfully. However, if the workflow is used to create 50 VMs at once, the job fails. Which of the following is the MOST likely cause of the issue? (Choose two.)
A systems administrator needs to modify the replication factors of an automated application container from 3 to 5. Which of the following file types should the systems administrator modify on the master controller?
While investigating network traffic, a cloud administrator discovers the monthly billing has increased substantially. Upon further review, it appears the servers have been compromised, and sensitive files have been exfiltrated. Which of the following can be implemented to maintain data confidentiality?
A cloud security engineer needs to ensure authentication to the cloud pro-vider console is secure. Which of the following would BEST achieve this ob-jective?
A systems administrator is configuring a storage system for maximum performance and redundancy. Which of the following storage technologies should the administrator use to achieve this?
A company has hired a security firm to perform a vulnerability assessment of its environment. In the first phase, an engineer needs to scan the network services exposed by the hosts. Which of the following will help achieve this with the LEAST privileges?


